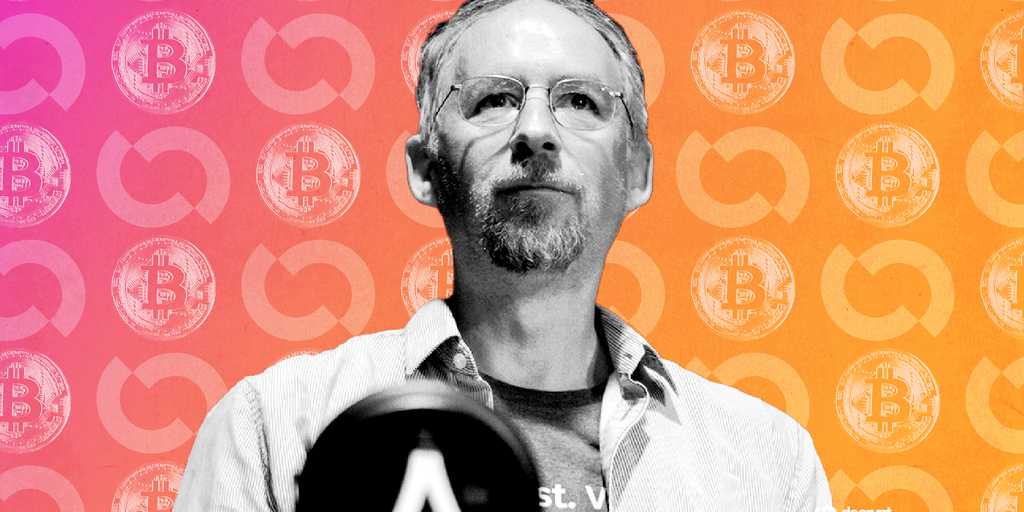
Adam Back Backs Opt-In Quantum Safeguards for Bitcoin, Challenges BIP-361’s Freeze Plan
At Paris Blockchain Week, Adam Back urged optional quantum upgrades for Bitcoin, countering BIP-361’s phased coin freeze as Google research flags 6.9M BTC at risk, including Satoshi’s.
Because Bitcoin
April 16, 2026
Bitcoin’s next security upgrade isn’t just cryptography—it’s governance. At Paris Blockchain Week, Blockstream CEO Adam Back argued for opt-in, quantum-resistant paths rather than preemptive freezes of legacy coins. His case landed one day after BIP-361 was updated in Bitcoin’s repository, proposing a phased soft fork that would sunset legacy signatures over five years and ultimately immobilize coins that don’t migrate—capturing even Satoshi-era balances.
The timing matters because the risk curve just steepened. New work from Google Quantum AI indicates that breaking elliptic curve cryptography could require under 1,200 logical qubits; on a superconducting platform, fewer than 500,000 physical qubits might be enough to compromise Bitcoin signatures in minutes—a roughly 20x drop from earlier estimates. Google and Caltech researchers now frame the horizon in years rather than decades. By their count, about 6.9 million BTC are exposed, including roughly 1.7 million from early mining rewards attributed to Satoshi Nakamoto.
The fault line isn’t “quantum or not”; it’s how Bitcoin should move. BIP-361—“Post Quantum Migration and Legacy Signature Sunset,” authored by Jameson Lopp and five others—codifies a default migration with a backstop: coins that don’t switch to post-quantum addresses get frozen. Back favors a different sequence: introduce optional primitives, let wallets, exchanges, and custodians roll forward voluntarily, and reserve coercive measures for an unmistakable emergency.
Why start optional? Because Bitcoin’s credibility often hinges on minimal governance discretion. Freezing long-dormant UTXOs, even for security, sets a powerful social precedent: rules can be changed against non-participants. That may look prudent to engineers but reads differently to capital allocators whose trust depends on predictable property rights. Once the network establishes that coins can be rendered unspendable for “safety,” policymakers and adversaries will test that lever for other aims—sanctions, censorship, clawbacks. Optional upgrades preserve neutrality while still hardening the attack surface as market actors migrate.
The counterargument is obvious: optionality leaves stragglers exposed, and attackers will target the weakest links. That’s where credible signaling and contingency design matter. Back underscored that the community has, in past crises, coordinated fixes within hours; urgency can focus attention and produce consensus without preemptively rewriting ownership rules. You don’t want to gamble on coordination, but you also don’t want to normalize it.
Several mitigation ideas try to square this circle. BitMEX Research outlined a “canary fund” of vulnerable coins: only if that address is spent (a strong sign of a live quantum break) would a network-wide freeze trigger. Others are exploring transaction formats that achieve quantum resistance without any fork at all. Beyond Bitcoin, ecosystems like Ethereum, Solana, Naoris Protocol, and Circle’s Arc Network are running their own experiments with post-quantum security, offering implementation lessons but not a governance template for Bitcoin.
If the risk window keeps compressing—Google’s estimates imply it might—Bitcoin’s upgrade path should probably evolve in stages:
- Ship opt-in post-quantum address types and wallet tooling now; let exchanges and custodians lead migrations. - Establish public telemetry and a clear escalation policy (e.g., canary-based triggers), so markets understand exactly when stronger measures activate. - Stress-test fee markets and mempools for a high-volume migration scenario to avoid adversarial congestion during a scramble. - Keep any freeze authority explicitly contingent, time-bounded, and socially costly to invoke.
The technical work—picking and implementing a mature post-quantum signature scheme, optimizing size/fees, and integrating with Taproot—is challenging but tractable. The harder piece is choosing incentives that upgrade security without rewriting Bitcoin’s social contract. Today’s discussion isn’t just about qubits; it’s about whether the network maintains its bias for voluntary coordination until a genuine signal forces a different call.
